Have you suffered a hacking attack in the last 12 months? You're not alone. 75% of organizations are in the same boat as you.
Cyberattacks of all kinds have been on the rise and have multiplied over the last few years. The goal of these web hackers is to collect information that is sensitive or important enough to be used against you, to force you to pay them a sum of money in exchange or to resell them to criminals.
To get you started, here are some impressive figures from a study conducted by the Ponemon Institute last October on Benelux companies that have experienced a cyberattack on their networks and systems over the past year:
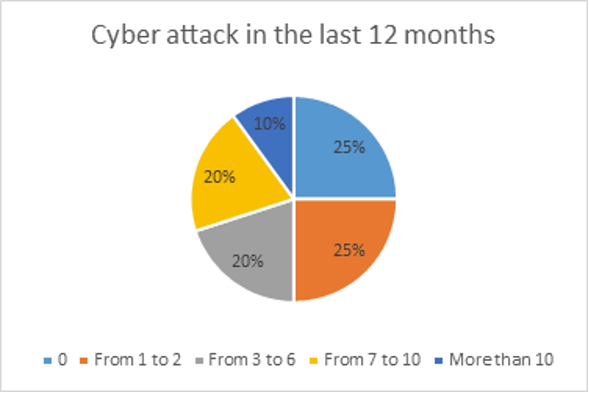
In summary, over the last 12 months, no less than 3 out of 4 companies have reported being attacked. Of these 3 companies, 1 of them has even suffered more than 7 attacks.
Why are these attacks more numerous?
In 2020, the Covid crisis has not only had health and financial impacts. It has brought with it on the one hand, an increase of telework, and on the other hand, a flood of hospitals and health care.
The risk of cyberattacks in organizations increases with containment and remote working. People who work from home are more vulnerable to attacks. They are more numerous and hackers often try to attract the attention of their victims with topical issues such as the coronavirus. It's been proven that employees have a greater tendency to click on malicious links, while they are not 'inside' the organization.
Against their will, healthcare institutions have become an interesting target for criminals as well. They are betting that the hospitals will not take the risk of refusing to pay a ransom, if that could have potentially dramatic consequences for the patients at a time when the pandemic is still very much alive.
What are the most common types of attacks?
The 2 most frequent types are still phishing and ransomware. In both cases, the attack is targeted towards the end user. This means they don't directly attack the servers, but they use an employee to get 'inside' the system.
Ransomware is software allowing the hacker, a recovery of all the data of the client or server followed by an encryption of the totality. After a simple click on a link or an attachment, the user instantly loses access to all his data and is obliged to pay the ransom to recover it.
Phishing is spam. The hacker pretends to be a trustworthy person via a seemingly innocuous email. In this email, this person asks the user to update personal data on a site that looks authentic but is not at all real. Once encoded, the hacker will be able to use all the information as he wishes.
How to protect yourself?
Here are a few tips that can reduce exposure to the attacks mentioned above:
-
At the Endpoint Protection level, move from traditional to Next-Gen.
It is high time to choose a "Next-Gen" Endpoint Protection, i.e. based on machine learning and automation rather than signatures like a traditional antivirus. It is no longer necessary to update signatures to get the maximum level of protection.
-
At the Phishing level, choosing Sandboxing
Anti-spam solutions based on state-of-the-art technologies such as Sandboxing prevent all ransomware, trojans and other viruses and malware threats from entering your network through the messaging channel. This involves opening attachments received by e-mail in a test environment to analyze their behavior.
-
At the level of your users, transform them into a human Firewall.
Today there are solutions to help you deliver the right training to the right people at the right time, transforming your end users into a strong last line of defense to identify cyberattacks and protect your organization. The goal is to be impactful, recurring and efficient.
Of course, this is not an exhaustive list. Other important elements remain applications: Backup, Firewall, MFA, VPN,...
For more information on any of these topics, please do not hesitate to contact us.
Want to know more? Reference: