IPSec VPN are common to secure connectivity between networks. However maintaining many of them can be cumbersome, so why not take shortcuts?
Securing network connections with IPSec VPN has been popular for decades. When connectivity only involves 2 sites which needs to talk to each other, it's pretty straight forward. However, when moving to more than 2 sites, the situation gets more complicated.
VPN with multiple sites
There are 2 main options for making a VPN design with multiple sites:
1. Hub and Spoke
In this scenario, one site is acting as the "Hub" (central site) and all other "Spokes" sites (remote sites) connect to it. The amount of tunnels required is limited to the total of sites -1 (7 sites in total = 6 tunnels).
The major drawback of this design is that all connections between Spokes sites are going through the Hub site. This means that the hub site has to be oversized to handle this extra load (processing power + line speed) and it introduces additional latency.
2. Full Mesh
In this scenario, each site is connected to all others sites.
While it counter the drawback of the "hub and Spoke" design, it has its own major drawback : the total tunnels.The amount of tunnels can be calculated with this formula (n = number of sites) : n*(n-1)/2
For a small number of sites, this is manageable, however it quickly tends to increase the complexity and the provisioning efforts become huge.
For the above example of 7 sites, the number of tunnels would be 21 tunnels. Adding a single site would total 28 tunnels.
Not to mention "hybrid" "ad hoc" solutions, based on a Hub and Spoke design, but with some direct Spoke to Spoke tunnels manually created whenever needed...
Is automation the solution?
You may think that automating - via scripting or with a central management system - the deployment of these tunnels gives you the advantage of full mesh without any drawback. Although you are partially right, there are still drawbacks to consider:
-
Increase of configuration: The size configuration still increases on every sites.
-
Increase of system load: Maintaining all tunnels and configurations requires extra resources.
-
Deployment risk: every time you add a new site, you have to make sensitive configuration changes on ALL your devices.
ADVPN
Fortunately, Fortinet offers us a solution: ADVPN. Auto Discovery VPN.
ADVPN aims to give you the best of both worlds. The base configuration is similar to Hub and Spoke with the ability to create shortcuts tunnel between spokes dynamically on demand.
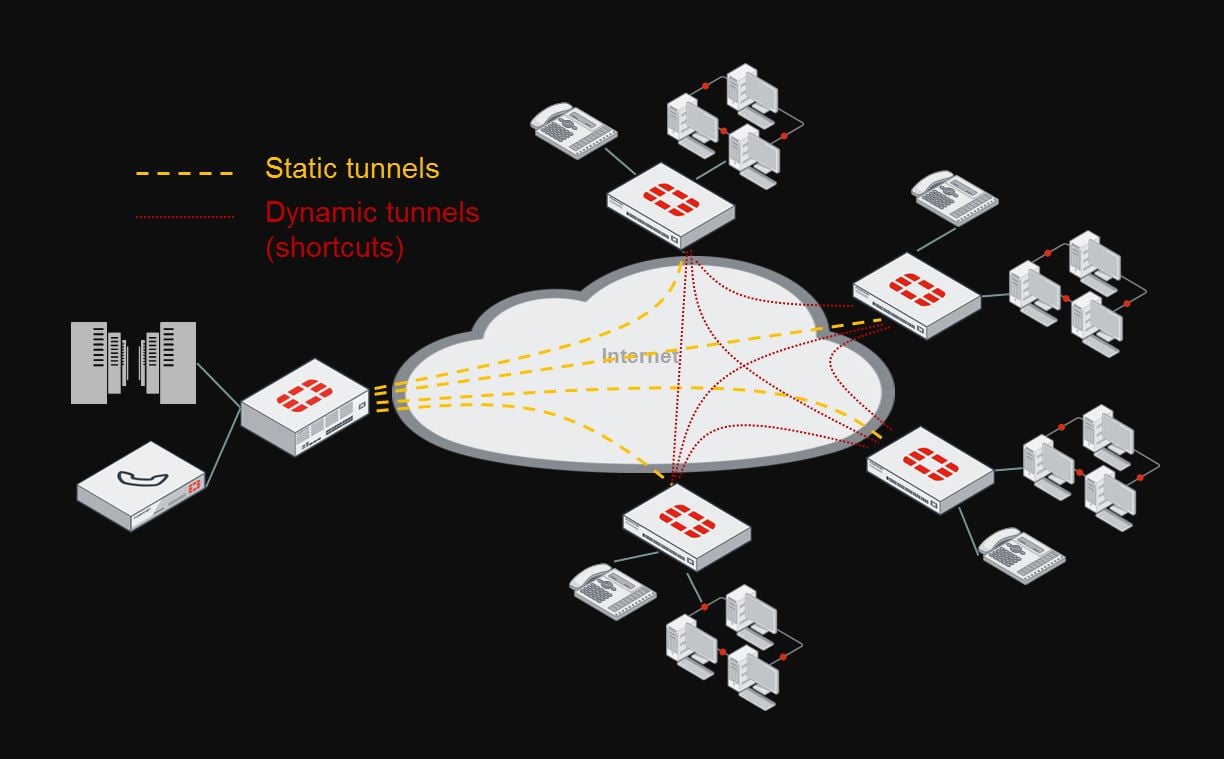
ADVPN uses IPSec to secure the communication and iBGP to exchange routes dynamically.
Introducing a new Spoke in the topology results in near zero-touch provisioning on the Hub and no provisioning at all on existing Spokes.
The final result is similar to what you can achieve with Cisco DMVPN using NHRP.
Supported devices
ADVPN is supported on all Fortigate running FortiOS 5.4 or more.
The ability to use ADVPN is automatically included and does not require any additional licenses.
Interested?
Get in touch with us and we will be happy to help you optimizing your multi-site VPN connectivity with Fortinet and ADVPN!